It's Time to Rethink Your Approach to Data Breach Response
When an adverse event occurs, organizations must quickly assess whether data was compromised and if that data set contained personally identifiable information (PII) or protected health information (PHI). Then, depending on a variety of other factors — including jurisdictional and industry-specific regulations — the incident may be legally determined to be a breach.
The incident response framework is comprised of several different phases and processes. This guide is a deep dive into one segment: data breach response.
Request this guide to learn:
- How to determine whether a privacy incident rises to the level of a data breach
- Steps to follow for an accurate and successful data breach response
- The impact of upfront processing and data mining on overall time and cost
- Challenges that response teams face at each phase, and how to overcome them
Get the Guide
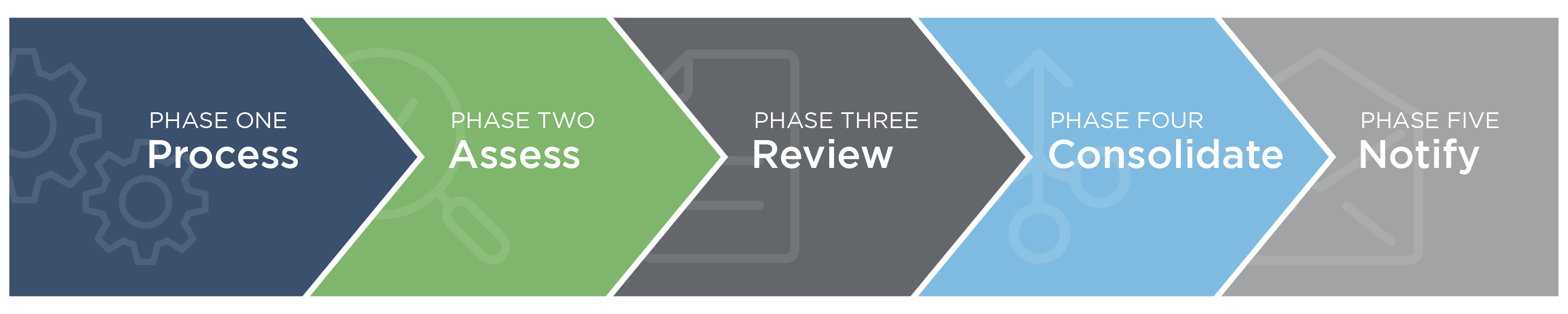
Explore the 5 Phases of Data Breach Response
Follow Canopy's workflow for the fastest & most efficient response to a cyber incident, from processing & assessing data through to notifying authorities and affected individuals.