- Resources
- Data Mining: Culling Case Study
Canopy Reduces Review Population by 89%, Saving Response Team 2,000 Hours
The Challenge
A U.S.-based online retailer experienced a business email compromise (BEC) resulting in 186,479 compromised documents. The response team first tried data mining via traditional ediscovery methods, which flagged 48% of the data set for PII Review. The project lead suspected this number was too high and did not want to review potentially thousands of unnecessary documents.
The Solution
The team enlisted Canopy's Data Breach Response software. Its advanced machine learning models automatically detected and validated over 70 different types of personally identifiable information (PII). The application’s powerful image and document classification tools helped further guide the response team’s strategy and focus their review efforts.
Original Data Set: 186,479 Documents
The Result
-
Detected and validated over 70 types of potentially-reportable PII elements
-
Clearly indicated which documents contained PII
-
Image and document classification tools provided insight beyond the detection of concrete PII elements
-
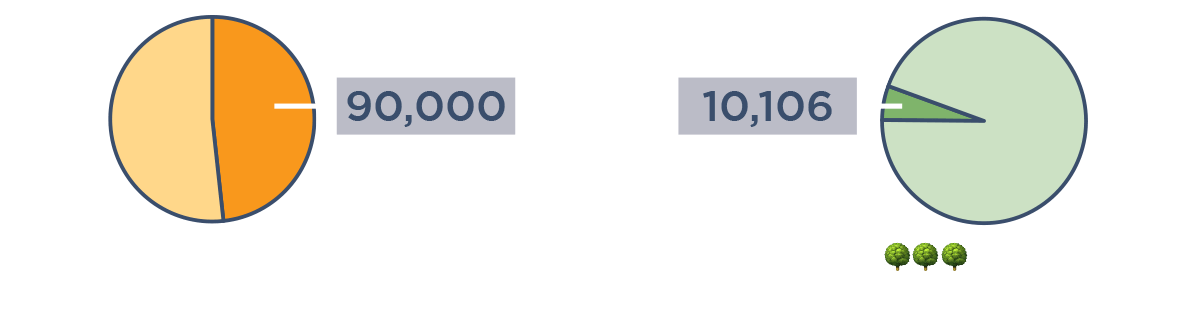
Correctly flagged just 10,106 documents as needing PII Review — 89% fewer than were initially flagged by ediscovery methods
-
Saved response team 2,000 review hours
Zero in on PII to Save Time & Notify Faster

79,894 documents
incorrectly flagged via ediscovery methods

90 seconds
average time to review each document

2,000 hours
saved with Canopy
Request Data Mining Case Study
See how one response team saved 2,000 hours with Canopy.
Request a Demo
See how Canopy's Data Breach Response software leverages machine learning at every step, from PII detection through to generating a notification list.
Get These Results for Your BEC Response
Request your personalized demo to see how Canopy's AI-powered solution can transform your workflow.